There has been a discussion about quantum computers being able to break encryption almost since the beginning of their history. One of the very first “quantum algorithms” that were developed for quantum computers many years before anyone even started building a quantum computer was actually encryption-breaking algorithms.
One algorithm, called Shor’s algorithm, quantum can completely break RSA and elliptic curve cryptography as soon as the quantum computer has enough (logical) qubits to do that. The other, called Grover’s algorithm, can drastically reduce AES encryption from 128-bits to 64-bits, which can then be broken by run-of-the-mill PCs.
You can attempt to increase the bits on each encryption algorithm and try to defend yourself that way against quantum computers, but once quantum computers can break the lowest levels of encryption, we should be only years away before they break the strongest versions of these encryption algorithms, too.
The good news is that thousands of logical qubits will be needed to achieve break what are currently the most common encryption algorithms in use.Researchers from Canadian company Krypterra believe that we’d need 2,953 logical qubits to break AES-128 and 6,681 logical qubits to break AES-256. Similarly, we’d need 4096 logical qubits to break RSA-2048.
But what are logical qubits anyway? Here comes the even “better” news in regards to encryption — Krypterra researchers say that to get thousands of logical qubits we’d need millions of physical qubits, or the same type of qubits Google, IBM, Intel, and others currently claim to have. Google itself has said before that quantum computers get truly interesting when we reach somewhere between 100,000 and 1 million qubits.
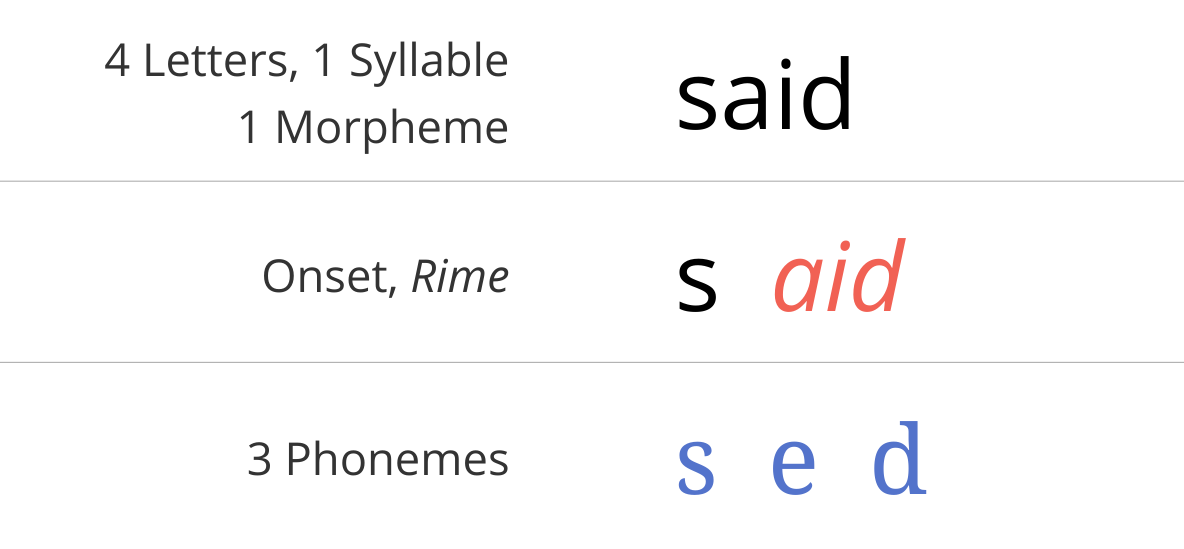
e = get, head
Dive into said